Member-only story
“Debunked: The Truth about mediaanalysisd and Apple’s Access to Your Local Photos on macOS”
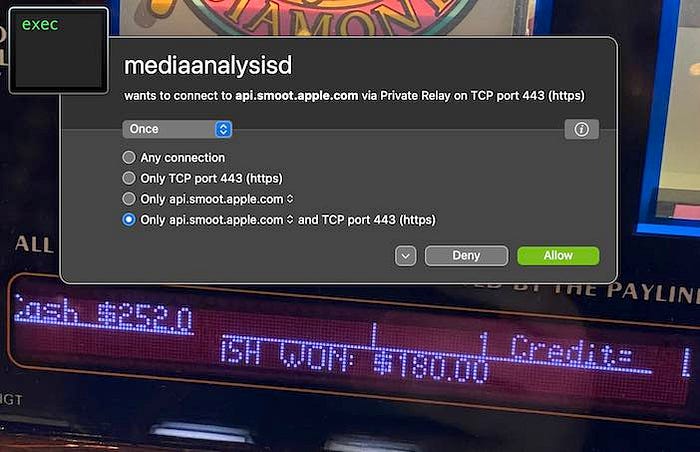
A recent thread on Twitter raised concerns that the macOS process mediaanalysisd, which scans local photos, was secretly sending the results to an Apple server. This claim was made by a cybersecurity researcher named Jeffrey Paul. However, after conducting a thorough analysis of the process, it has been determined that this is not the case.
The mediaanalysisd process is a background task that starts every time an image file is previewed in Finder, and then calls an Apple service. The process is designed to run machine learning algorithms to detect objects in photos and make object-based search possible in the Photos app. It also helps Finder to detect text and QR codes in photos. Even if a user does not use the Photos app or have an iCloud account, the process will still run.
The analysis of the mediaanalysisd process revealed that it does not access any suspicious resources. The content of its framework, MediaAnalysis.framework, clearly shows that the process is used for object detection in photos, and its binaries file contains a huge list of objects the model is trained to detect. Some examples of these objects include cars, people, and animals.
Additionally, even if a user does not have an iCloud account, their Mac still needs to call Apple services for things like checking for updates to the macOS. However, the network traffic sent and received by mediaanalysisd was found to be empty and appears to be a bug. The data shown by Activity Monitor about this process is only the data needed to establish an HTTPS channel with the server.
In conclusion, the mediaanalysisd process does not send any data to Apple about local photos. The network call that raised concerns is a bug. Apple has since released macOS 13.2, which has fixed this issue, and the process no longer makes calls to Apple servers. It is recommended that users update their Mac to this version to…
